
Hackers Exploit Weak Remote Desktop Protocol Credentials
Authentication
,
ID & Access Management
,
Ransomware
Darknet Markets Sell Harvested RDP Credentials for as Little as $6
Many enterprises use remote desktop protocol to remotely administer their PCs and mobile devices. But security experts warn that weak RDP credentials are in wide circulation on darknet marketplaces and increasingly used by ransomware attackers.
See Also: How to Scale Your Vendor Risk Management Program
Opportunistic attacks against RDP server and endpoint credentials “have been around for many, many years,” Paul Pratley, head of investigations and incident response at MWR InfoSecurity in London, tells Information Security Media Group. Attackers now often use botnets to automatically search out internet-connected devices with exposed RDP ports and them hammer them with brute-force username and password guesses until their attack tools find a match, he says. Many RDP credential harvesters will then sell this access to others.
Stolen RDP credentials “used to be used to distribute things like DDoS [distributed denial-of-service] malware and bitcoin mining malware” inside enterprises, Pratley says. Since late 2015, however, ransomware attackers have been increasingly using RDP, he points out.
What is RDP?
The enduring appeal of poorly secured RDP is easy to understand. The proprietary protocol developed by Microsoft provides graphical access to a client from a server via encrypted TCP traffic. Clients for RDP are available for most versions of Microsoft Windows, as well as Linux, Unix, macOS, iOS, Android and other operating systems. By default, an RDP server listens on TCP port 3389 and UDP port 3389.
Poorly secured RDP gives hackers a potential entry point into enterprise networks. “Once a hacker secures login credentials for RDP access, he or she effectively owns the system where the RDP server is installed,” Vitali Kremez, a cybercrime intelligence analyst for threat intelligence firm Flashpoint, says in a blog post. “In addition to being able to launch external attacks and move laterally within networks, attackers are then able to plant malicious software, exfiltrate data and/or manipulate network settings.”
Attackers have used RDP to spread numerous strains of crypto-locking ransomware, including Crysis and Bitpaymer (see Scottish Hospitals Hit by Bitpaymer Ransomware).
But such outbreaks may be the final stage of an intrusion that has already endured for weeks or months, says incident response expert David Stubley, CEO of cybersecurity consultancy 7 Elements in Edinburgh, Scotland.
“We have seen cases where the RDP endpoint has been compromised by a different threat actor and access to the compromised site maintained for a period of weeks before being used for a ransomware attack,” Stubley tells ISMG. “Presumably they sold access once finished with whatever they wanted from the compromised server or environment.”
To help prevent RDP servers and clients from being compromised, security experts recommend that organizations always secure RDP using strong and complex passwords to block brute-force attacks, monitor for any unusual network behavior and regularly audit ports to ensure that there are no open and unsecured RDP or SSH ports.
For Sale: RDP Server Access
Organizations that fail to follow this guidance may find their RDP server credentials for sale on darknet marketplaces – cybercrime e-commerce sites reachable only via the anonymizing Tor browser (see Police Seize World’s Two Largest Darknet Marketplaces).
In June 2016, security firm Kaspersky Lab warned that 250,000 credentials for RDP servers around the world appeared to be for sale for as little as $6 each on the Russian language cybercrime and forum and marketplace called xDedic. After the report was released, xDedic appeared to close up shop before reopening as a Tor site.
Flashpoint’s Kremez analyzed a publicly exposed dataset from xDedic that contained RDP access information for 85,000 servers and found that the most compromised sectors were education, healthcare, legal and aviation. And the United States, Germany and Ukraine were the most targeted countries, based on the number of compromised RDP credentials contained in the data set.
“The prolific threat actor ‘thedarkoverlord,’ notorious for targeting healthcare entities, is believed to have leveraged this data set for at least some of their breaches,” Kremez says in his blog post (see Cyber Ransom Group Hits Soft Targets: US Schools).
While RDP access provides convenience for IT shops that want to remotely administer PCs, using it carries risks “given that remote attackers – including the prolific threat actor ‘xDedic’ – may be able to guess or brute force the login credentials,” Kremez says.
Ultimate Anonymity Services
But xDedic isn’t the only RDP shop in town. Another player called UAS – for “Ultimate Anonymity Services” – has been online since Feb. 16, 2016, offering more than 35,000 brute-forced RDP servers for sale as well as Socket Secure – SOCKS – proxies for client/server networks, according to Flashpoint. The site operates in both Russian and English.

Flashpoint’s Kremez and fellow cybercrime intelligence analyst
The researchers found the greatest number of individual RDP credentials for sale for the following countries:
- China: 7,216 RDPs
- Brazil: 6,143 RDPs
- India: 3,062 RDPs
- Spain: 1,335 RDPs
- Colombia: 929 RDPs
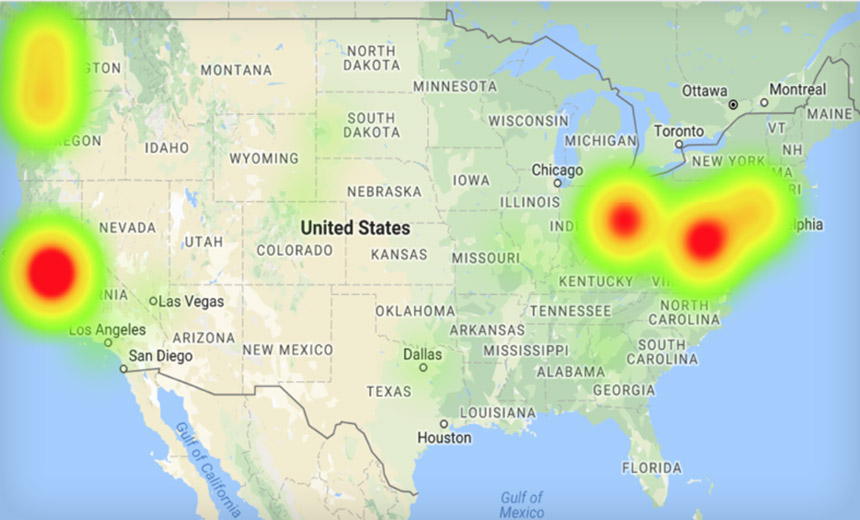
UAS also lists about 300 RDPs for U.S. servers, mostly in parts of Virginia, Ohio, California and Oregon.
“Most of the RDPs are geographically aggregated across a few specific ZIP codes,” Rowley and Kremez say. “Such concentration possibly indicates opportunistic exploitation of a handful of companies utilizing multiple RDPs; it is likely that these companies have lax security measures, leading to a greater number of vulnerable RDPs.”


